My Very Own CA, How Sweet :)
Just splurging this down here for next time, as I had to go trawling for this info in various old text files today… Very related to https://blog.oholics.net/creating-simple-ssl-certificates-for-server-authentication-using-openssl/, but using my own CA rather than an enterprise or public CA.
I was working in my lab today to setup SLDAP on my lab domain controller. I was doing this to validate the syntax of ldapsearcher, on a Ubuntu machine, in different cases and also to see if I could determine the reason I was seeing a particular error (see https://blog.oholics.net/ldapsearch-syntax-for-simple-ldap-and-sldap/).
I want to KISS (keep things simple stupid), so was going to use the rootCA that I setup with OpenSSL a few years ago (running on my Windows machine).
Back then I ran the following commands to create the “top level” Root CA certificate and Private Key:
openssl genrsa -out rootCA.key 2048
openssl req -x509 -new -nodes -key rootCA.key -sha256 -days 1024 -out rootCA.pem
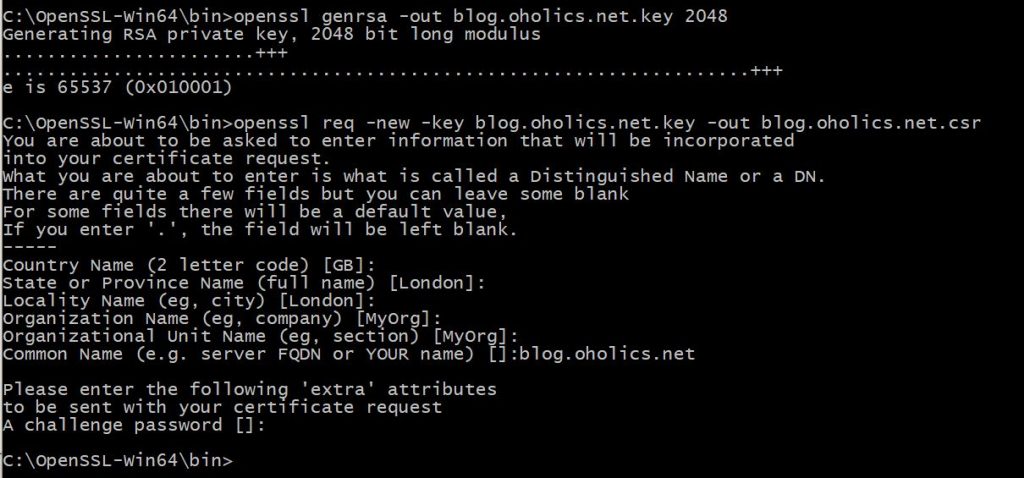
To generate my domain controller certificate today, I used (with an edited openssl.conf file of course):
openssl genrsa -out dc.oholics.net.key 2048
openssl req -new -key dc.oholics.net.key -out dc.oholics.net.csr
openssl x509 -req -in dc.oholics.net.csr -CA rootCA.pem -CAkey rootCA.key -CAcreateserial -out dc.oholics.net.crt -days 500 -sha256
openssl pkcs12 -export -out dc.oholics.net.pfx -inkey dc.oholics.net.key -in dc.oholics.net.crt -certfile dc.oholics.net.crt
On the domain controller, I installed the dc.oholics.net.pfx file into the computer personal store and the rootCA.pem into the computer trusted root certification authorities store. Reboot and done..
###################################################################################
Minor edit…. I originally created the root certificate a rather long time ago… Today I discovered it was expired, thus the few certificates issued by it are also fubared.
Simple fix (where I don’t have to publish anything very far or wide):
Regenerate the rootCA certificate using the original key:
openssl req -x509 -new -nodes -key rootCA.key -sha256 -days 10240 -out rootCA.pem
Then start re-issuing those certificates that I was actually using (again using the keys and csr’s previously used:
openssl x509 -req -in MyImportantCert.csr -CA rootCA.pem -CAkey rootCA.key -CAcreateserial -out MyImportantCert.crt -days 5000 -sha256
openssl pkcs12 -export -out MyImportantCert.pfx -inkey MyImportantCert.key -in MyImportantCert.crt -certfile MyImportantCert.crt
Note the extra 0’s on the number of valid days, shouldn’t have to do this again for a good while 🙂